Microsoft has just taken a significant step forward in the evolution of desktop virtualisation with the latest announcement around Azure Virtual Desktop Hybrid. But for me, the most interesting part isn’t just “more flexibility”. It’s what this means for customers who have been stuck between cloud ambition and on-prem reality.
There’s always a running joke that every year is “the year of VDI”. But honestly, AVD Hybrid feels like one of the biggest shifts I’ve seen in this space for a long time. This announcement also makes the broader Windows in the Cloud story much clearer. If you want the simplest and fastest route to Windows in the Cloud, that’s still Windows 365.
AVD Hybrid sits differently. It’s about flexibility, infrastructure reuse, and meeting customers where they are, while supporting a more gradual transition into Azure.
What is AVD Hybrid (in plain English)?
Historically, AVD has meant one of two things:
- Session hosts in Azure
- Or more recently, session hosts on Azure Local
AVD Hybrid changes that.
It allows you to run AVD session hosts anywhere and still connect into the Azure control plane. At the core of this is Azure Arc. Instead of forcing workloads into Azure, Arc brings your infrastructure into Azure.
That means:
- On-premises VMs
- Existing hypervisors like VMware ESX, Nutanix, and Hyper-V
- Even physical servers
…can now act as AVD session hosts.
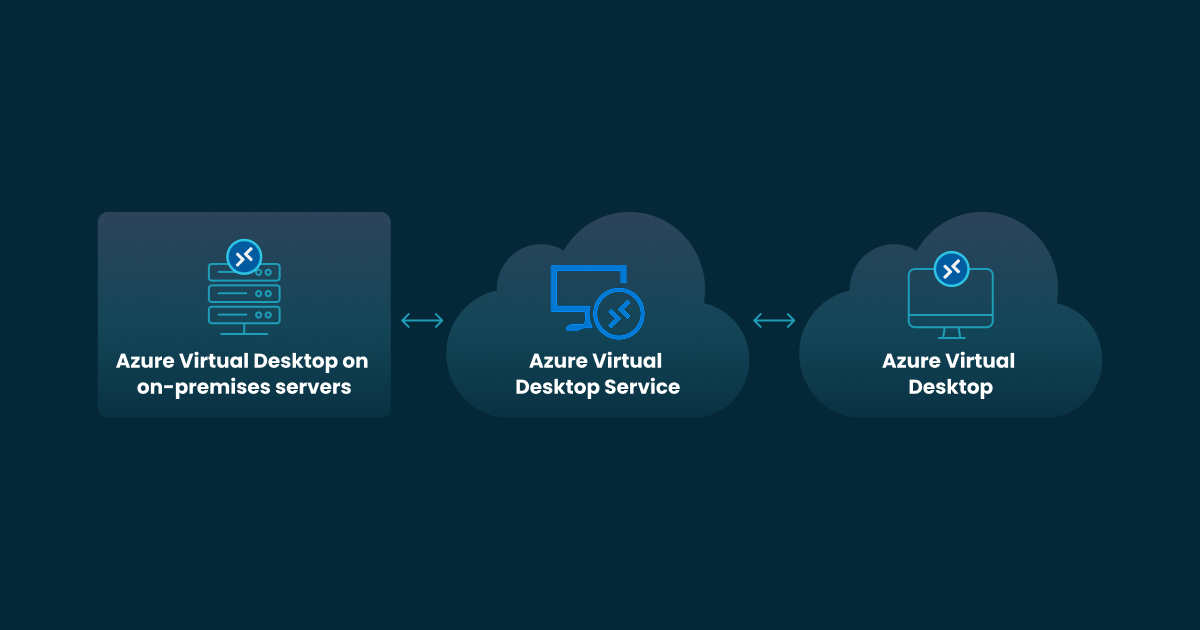
The Architecture Shift (this is the big bit)
AVD Hybrid introduces a clean separation:
- Control plane stays in Azure
- Session hosts (compute) can run anywhere
This effectively gives you cloud-managed VDI, delivered from your own datacentre. Your session hosts register via Arc and connect directly to the AVD service in Azure.
So you still get:
- Brokering
- Gateway
- Identity integration
- Management
…but without requiring compute to sit in Azure.
Why This Matters (based on real customer conversations)
This unlocks scenarios I’ve seen customers struggle with for years, especially across healthcare, government, education, and organisations with existing VDI investments.
1. Data residency and compliance
Keeping workloads on-prem while still using a cloud control plane is huge for sectors like healthcare, policing, and government.
2. Latency-sensitive workloads
If your apps need to sit close to users or data, you no longer need to compromise.
I’ve already seen scenarios involving complex multicast requirements and clinical applications where this becomes really important.
3. Existing VDI investments
Customers can reuse existing infrastructure instead of ripping and replacing.
4. Gradual cloud migration
This is probably the biggest one.
AVD Hybrid gives customers a stepping stone rather than forcing a big-bang migration into Azure.
AVD Hybrid vs Azure Local (important distinction)
It's easy to confuse the two, but they're quite different:
| Capability | Azure Local | AVD Hybrid |
|---|---|---|
| Infrastructure model | Microsoft-defined stack | Any Arc-enabled infrastructure |
| Hypervisor flexibility | Limited | Broad (vSphere, AHV, Hyper-V, physical) |
| Approach | Cloud-adjacent | Truly hybrid |
Azure Local is still a strong option, especially for standardised deployments.
But AVD Hybrid is about meeting customers where they are.
What to Watch Next
AVD Hybrid is still early, but I expect rapid movement across the ecosystem.
The biggest area to watch will be the management and operational layer around Hybrid deployments.
For organisations looking at production adoption, I’d strongly recommend considering platforms and partners like Nerdio, Login VSI, ControlUP and Nutanix:



Microsoft provides the platform, but these vendors help build the operational maturity layer around it, especially as environments scale.
Deployment
Quick-start deployment guide for Azure Virtual Desktop Hybrid
OK, Enough of the Opinions. Let's Build It.
Below is a full technical walkthrough of how I deployed AVD Hybrid Environments end to end, including two PowerShell scripts I built to automate the entire process.
Supported Platforms and Identity
| Virtual Machine | Physical Machine | |
|---|---|---|
| Windows Server 2016–2025 | ✅ | ✅ |
| Windows 11 Enterprise (single-session) | ✅ | ❌ |
| Windows 11 Enterprise Multi-Session | ❌ | ❌ |
Session hosts can be Entra joined, ADDS joined, or hybrid joined.
Public Preview notice: AVD Hybrid Environments is currently in public preview. Host pools must be configured as validation environments. Not recommended for production workloads until General Availability.
My Test Environment
For this deployment I used:
- Session host: Windows 11 Enterprise VM running in VMware Workstation Pro
- Identity: Entra joined and enrolled into Intune via a Device Enrolment Manager (DEM) account
- Azure: New tenant with a fresh subscription
- Location: UK South for all resources
Prerequisites
Before you start, make sure you have:
- An Azure subscription with Owner or Contributor access
- PowerShell 5.1 or later (Windows PowerShell ISE works fine)
- The session host VM must have outbound internet access to AVD endpoints and Azure Arc endpoints
- The VM must be Entra joined, ADDS joined, or hybrid joined before the Arc extension is installed
The Scripts
I've broken the deployment into two scripts to keep things clean and repeatable:
Deploy-AVDHybrid-Greenfield.ps1 - Run once from your admin machine. Sets up all the Azure infrastructure and outputs a config file.
Deploy-AVDHybrid-SessionHost.ps1 - Run on each session host VM. Reads the config file and handles everything from Arc agent install to AVD extension deployment.
Both scripts are safe to re-run and automatically detect existing resources.
Part 1 – Greenfield Deployment (Run from your admin machine)
Section 0 – Variables
Open Deploy-AVDHybrid-Greenfield.ps1 and update Section 0 with your own values:
$TenantId = "YOUR_TENANT_ID"
$SubscriptionId = "YOUR_SUBSCRIPTION_ID"
$AdminAccount = "YOUR_ADMIN_UPN"The resource names, locations, and group names are all pre-set with sensible defaults using an AVD- prefix. Change these if you want a different naming convention.
Section 1 – Install Modules
Installs the required Az PowerShell modules if not already present. Also installs the NuGet provider silently to avoid interactive prompts.
Az.Accounts, Az.Resources, Az.DesktopVirtualization, Az.ConnectedMachineSection 2 – Authenticate
Opens a browser window to sign in to Azure and sets the correct subscription context. Confirms your context before you proceed.
Section 3 – Register Resource Providers
Registers Microsoft.HybridCompute and Microsoft.DesktopVirtualization. Unlike the private preview, the public preview no longer requires EUAP/canary region feature flags - standard Azure regions work throughout.
Run the validation lines until both return Registered before moving on.
Section 4 – Create Resource Groups
Creates two resource groups:
AVD-HostPool-RG- holds the AVD host pool, workspace, and application groupAVD-ArcServers-RG- holds the Arc-enabled session host resources
Both skip creation if the resource groups already exist.
Section 5 – Assign RBAC Roles
Assigns your admin account:
- Desktop Virtualization Contributor on the AVD resource group
- Azure Connected Machine Onboarding on the Arc resource group
Section 6 – Create AVD Host Pool, Workspace and App Group
Creates the host pool using the 2024-04-08-preview API version via Invoke-AzRestMethod. This is required because the standard New-AzWvdHostPool cmdlet uses an older API that doesn't support assigning a system-assigned managed identity - which is needed for AVD Hybrid.
Key settings:
- Host pool type: Pooled
- Load balancing: Breadth-first
- Validation environment:
true← required for public preview - Managed identity: System-assigned
The workspace and desktop application group are created and linked automatically.
Section 7 – Grant Managed Identity Reader Access
The host pool's managed identity needs Reader access on the Arc resource group so it can see the session host status. A future release will block session host availability if this is missing.
Section 8 – Create Service Principal and Config File
Creates a service principal (AVD-ArcOnboarding-SP) for Arc onboarding and generates a 24-hour registration token for the host pool. All credentials and configuration are saved to AVD-SessionHost-Config.txt on your Desktop - this is what the session host script reads automatically.
If the registration token expires before you onboard a VM, just re-run Section 8 to get a fresh one.
Section 9 – Create Entra User Group
Creates an AVD-Users group in Entra ID and assigns it:
- Desktop Virtualization User on the AVD resource group - so members can see and launch the workspace
- Virtual Machine User Login on the Arc resource group - so members can log into the Entra-joined session hosts
To add users: Entra ID → Groups → AVD-Users → Members → Add
Section 10 – Set Host Pool RDP Properties
Adds targetisaadjoined:i:1 as a custom RDP property on the host pool. This is required to allow connections from devices that aren't Entra joined to the same tenant, including the Windows App and web client.
Part 2 – Session Host Onboarding (Run on each VM)
Copy both Deploy-AVDHybrid-SessionHost.ps1 and AVD-SessionHost-Config.txt into the same folder on the VM. Open in PowerShell ISE or VS Code and run as Administrator.
Section 0a – Execution Policy
Sets the PowerShell execution policy to RemoteSigned for the current user if not already set. This is required to run the script - on a fresh VM it will be blocked by default.
If the script won't open at all, run this first in the PowerShell console:powershell
Section 0b – Load Config File
Reads all variables from AVD-SessionHost-Config.txt automatically. Validates that all required values are present and checks the registration token expiry. Stops with a clear error if the token has expired rather than letting it fail silently later.
Section 1 – Pre-install RDSH Role (Windows Server only)
On Windows Server, the AVD extension installs the Remote Desktop Session Host (RDSH) role which triggers a reboot. Pre-installing it here avoids an unexpected reboot mid-deployment. Automatically skipped on Windows 11.
Section 2 – Install Azure Arc Agent
Downloads and installs the Azure Arc Connected Machine agent (azcmagent). Checks if it's already installed and skips if so. Validates the installation before proceeding.
Run as Administrator - the MSI installer will fail silently without it.
Section 3 – Connect Arc Agent to Azure
Connects the Arc agent to Azure using the service principal from the config file. Includes two important checks:
- Status check - correctly parses
Agent Statusto distinguishConnectedfromDisconnected(a common source of false positives) - Tenant check - verifies the agent is connected to the correct tenant, not a previous one. Automatically disconnects and reconnects if the tenant doesn't match.
Section 4 – Deploy the AVD Extension
Installs the CloudDeviceExtension Arc extension which registers the VM as an AVD session host. This extension:
- Installs the AVD agent and boot loader
- Registers the machine in the host pool using the registration token
- On Windows Server, also installs the RDSH role (hence the pre-install in Section 1)
It can take up to 15 minutes after the extension installs for the session host to appear as Available in the host pool.
Section 5 – Validate
Checks the extension provisioning state and session host status in the host pool. If the host isn't visible yet, wait a few minutes and re-run this section.
Connecting to the Session Desktop
Once the session host shows as Available in the host pool:
- Add your user to the
AVD-Usersgroup in Entra ID - Open Windows App or browse to https://windows.cloud.microsoft
- Sign in with your Entra credentials
- You should see AVD-Workspace with a SessionDesktop tile
- Click to connect - sign in with your Entra credentials when prompted
Troubleshooting Tips
| Issue | Fix |
|---|---|
DomainJoinedCheck failed | Ensure the VM is Entra joined, ADDS joined, or hybrid joined before installing the Arc extension |
| Arc agent shows Disconnected | Re-run Section 3 of the session host script — it will detect and reconnect automatically |
| Session host shows Unavailable | Check SxSStackListenerCheck — try restarting the VM |
MetaDataServiceCheck failed | Semi-fatal in VMware/non-Azure environments — doesn't prevent connections |
| Registration token expired | Re-run Section 8 of the Greenfield script and copy the updated config file to the VM |
BadRequest on role assignments | Normal — Entra propagation delay. The script now includes a 15-second wait to mitigate this |
| MSI installer fails (error 1603) | Run PowerShell ISE as Administrator |
What's Next
This is just the foundation. From here you could:
- Add FSLogix profile containers using Azure Files with Entra Kerberos authentication
- Enable Single Sign-On via Microsoft Entra authentication for a seamless connection experience
- Configure Intune policies on the Entra-joined session hosts
- Scale out by running the session host script on additional VMs - no changes needed, just copy the two files
Scripts and Resources
- 📁 GitHub: https://github.com/bowkercloud/AVDHybrid
- 📖 Microsoft Docs: Deploy AVD Hybrid Environments
- 📖 Microsoft Docs: Entra joined session hosts in AVD
- 📖 Microsoft Docs: Azure Arc-enabled servers
Become a subscriber receive the latest updates in your inbox.